Back in December, Cyber Security firm Redscan published a report, based on FOI responses, showing that the NHS was apparently under investing in cyber security resources and training.
The NHS takes a lot of flak in the press, sometimes deservingly and sometimes not. I was struck by the fact that every time this news was reported the story quoted the Redscan report but not the NHS. I do not know if the NHS were asked to comment on the report, the articles did not say, but I would certainly understand if the NHS were not willing to engage in a conversation about it. I think the report is challenging the NHS on the wrong question.
Obviously, if the NHS Digital team have decided that there must be a standard, and the standard is not being met then this is newsworthy. But is there such as standard?
In fact I found two standards both now present in the Data Security and Protection Toolkit for 2019/20 that match those talked about in the press (the report referenced the previous version):
| Evidence Code | Assertion | Evidence Text - "NHS Trusts, CCG/CSUs and ALBs" |
| 3.2.1 | Staff pass the data security and protection mandatory test. | Have at least 95% of all staff, completed their annual Data Security awareness training in the period 1 April to 31 March? |
| 3.3.1 | Staff with specialist roles receive data security and protection training suitable to their role. | Provide details of any specialist data security and protection training undertaken . |
| 3.3.2 | The organisation has assessed its requirement for technical cyber security specialist staff and/or service. |
So for general staff training, covered in 3.2.1 there is a numeric standard to achieve, found wanting in the report. Fair enough. Good job Redscan.
On the other hand, with respect to the hiring of "technical cyber security specialist staff and/or service" there is no numerical standard as such. The nearest you get is a note requiring the review occurred in "the last Twelve months" which I expect means annually.
So the fact that Redscan identified expert:staff ratios as high as 1:2,582 or even 0:16,000 means nothing with respect to the Toolkit quoted above. While this sounds superficially concerning, much depends on what the non-specialists are up to.
The Toolkit is very broad, taking in the operation of networks, machine patching, user activities (such as what the doctors and nurses are doing) as well as the kind of applications and systems that are the bread and butter of most agilists. If network staff are patching devices and enforcing password policies, and doctors are keeping within the rules then this is a success despite the number of expert cybersecurity staff telling them to do it. Some cyber security staff will be more effective than others and all of them will have subtly different circumstances to work within. Staff ratios are not the primary measure of success, they are a proxy for success.
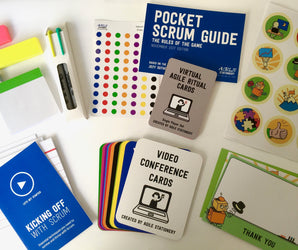
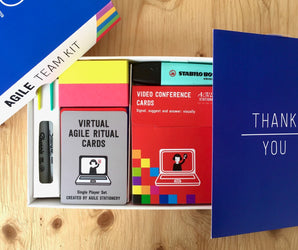
What we have learned through our efforts to support application developers and agile managers is that often getting non-specialists to bring their attention to a traditionally specialist problem is a great way to achieve progress.
For Quality Assurance specialisms this is called ShiftLeft, culminating in solutions like Specification By Example which test the requirements before the solution is designed. For operations the DevOps trend has meant developers going on pager duty and setting up status screens next to their build screens. For cyber security, this trend manifests itself in threat modelling games like Elevation of Privilege being played by developers during the design and build phase and security holes being filled long before anything is put in front of real users.
As an application developer I would be much more interested in metrics generated from commit logs and bug trackers showing how many people are reporting and fixing security issues.
If getting more eyes looking for security problems is your goal, then those people matter as much as security specialists. Perhaps security experts will end up taking on the role of the QA expert in modern agile: to coach teams and champion outcomes throughout the process and to support the entire team.