With much of the world suddenly working remotely, there is a good chance that your business is doing things online that it wasn't even dreaming of doing just a few weeks ago. Your assumptions about what can be taken granted and what cannot have certainly changed (in security terms, this is called your threat model). When updating your threat model, you must consider that when you are dealing with people’s data, the risk of accidentally ending up in pickle over privacy is significant.
Security and privacy (let’s call these together data protection) isn’t on top of everyone’s agenda – and it shouldn’t. There is a job that should be the top of your agenda, and if no one is getting the job done, then there is no payment, irrespective of how good the data protection is. I've been working for a long time on simple and effective ways to help technical teams keep to data protection rules by helping them avoid common pitfalls, while keeping the balance of letting them do their job effectively and not blocking them. I believe this approach allowed companies I’ve worked with to meet their GDPR and CCPA timelines, while not stopping the business at the same time. And these tools are still relevant in times of other drastic agenda changes.
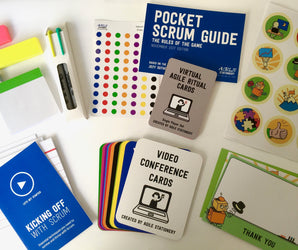
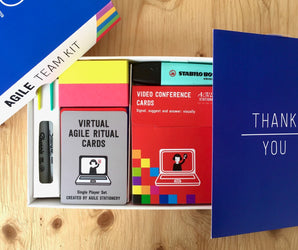
As one of these tools, let’s look at the Elevation of Privilege card game and the privacy extension. This is a very effective tool to convey basic data protection principles that engineers can directly translate into their daily work. Playing the game usually takes 2-3 hours for an average size project, and it is a very intensive exercise in terms of issues it can surface. During the game, as the mindset of engineers slowly adopts to thinking critically, your engineers will transform into your mini privacy advisory board and surface issues which might bother your end users as well.
Let's look at a company that has recently found itself in trouble and which you certainly also heard plenty of: Zoom.
Now, here I don’t want to analyze the severity of the issues or provide you with a verdict whether the use of Zoom is secure enough for your use or not. All I’m saying is that they received a lot of negative coverage, and I’m showing how the use of the Elevation of Privilege game could have helped with that.
Initially Zoom has been criticized for their lax language in their privacy policy. Some critics did a lot of guessing as to what they are trying to hide by the use of specific terms. They since updated their policy to be more specific.
At the same time, people highlighted Zoom’s attendee attention tracking feature, where hosts could see whether Zoom is placed into the background or not – this feature has been removed since as well.
An ongoing issue is the problem of Zoombombing, where people can easily guess meeting IDs and then disturb meetings they access. To avoid this, hosts can configure passwords for their meetings.
And then two researchers identified that Zoom was using a weak mode of the AES encryption algorithm, called ECB, and that keys used to set up the encryption could travel through servers in China, something not all customers might be happy with. Again, Zoom very actively addressed all identified issues.
There is much that is new, or at least unique about these issues, but the familiar privacy pitfalls are also present. Mapping these onto the Elevation of Privilege and privacy cards we see following:

Two of Privacy, your system does not ship by default with optimized, privacy-friendly settings: Zoombombing is easily mapped to this card, as setting a meeting to be joinable by everyone and allowing them to share their screen should be a specific decision someone needs to make, instead of it being the default configuration. Similarly, allowing hosts to track your attention should be prominently highlighted or turned into a configuration, instead of happening unknowingly.

Jack of Privacy, your system is processing personal data in countries which have weak privacy standards: There isn’t much to elaborate here. Apart from regulations and contractual protections, there are countries some people will feel uncomfortable about, and you need to give your users options.

Five of Information Disclosure, an attacker may be able to read a document or data because it’s encrypted with a non-standard algorithm: The use of AES-ECB has been discouraged for a long time. While strictly speaking AES-ECB is a standard form, a short discussion and investigation would have shown that it is weak.
This is just one way how common pitfalls can be detected. Depending on your processes, there are alternatives that let you dive deeper into doing data protection analysis or which rely more heavily on having dedicated champions in your teams. Whichever you chose, the hard part is to turn it into a regular exercise that is done for all new activities. Based on my experience, doing it via a card game is an effective means that will stick on everyone’s mind.